Chinese State-Sponsored Cyber Attacks

What Do Advanced Cyber Attacks Look Like? Cybersecurity is an ever-evolving battlefield, with state-sponsored attacks becoming increasingly sophisticated. The Australian Cyber Security Centre in conjunction with it’s allies in the UK, New Zealand and USA have released details of recent attacks attributed to the PRC Ministry of State Security (MSS) – known as APT40. These […]
Supplier Due Diligence: An Introductory Guide

In today’s digital age, organisations are more interconnected than ever, relying heavily on suppliers and third-party vendors to provide essential services and products. While this interconnectedness is great for operational efficiency, it also introduces significant cybersecurity risks. Undertaking appropriate due diligence on suppliers helps mitigate these risks and protect the organisation’s data. In this comprehensive […]
MFA Fatigue: The Shift to Phishing-Resistant Authentication

MFA Fatigue The Shift to Phishing Resistant Authentication It’s long been widely known that in the real world passwords alone are not a great way to authenticate users. Some people pick simple passwords that can easily be guessed. Others will re-use their company password for their login to a random quiz website run by a […]
No-Defender can deactivate windows defender
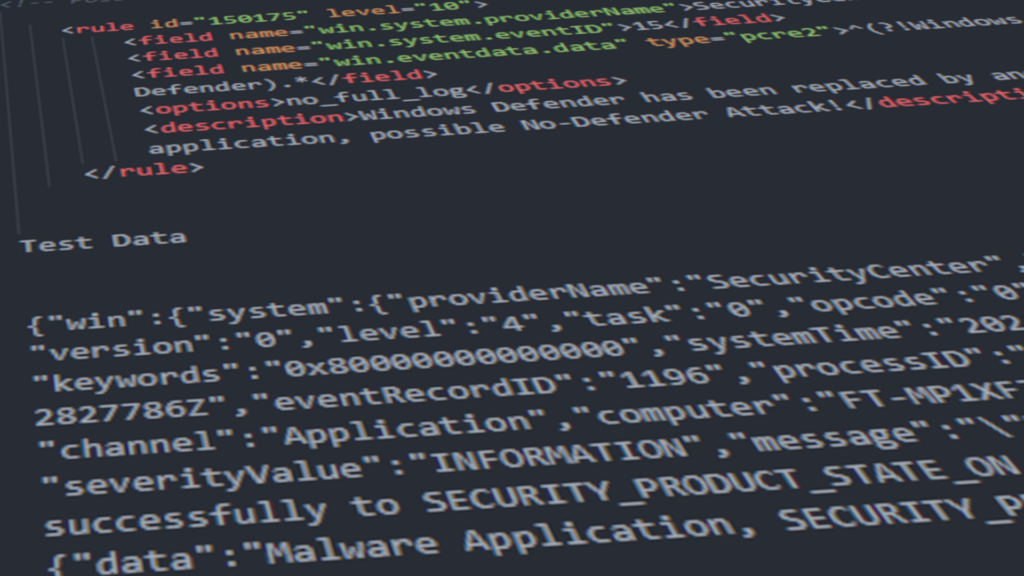
Last week a new tool was brought to my attention, No-Defender, a tool published on GitHub that can deactivate Windows Defender by exploiting the Windows Security Center (WSC) registration mechanism. The method is typically used by antivirus (AV) and endpoint detection and response (EDR) software to avoid conflicts with Windows Defender by becoming the primary security […]
Enhance Your Cybersecurity with Defend Train our Comprehensive Training Solution

Maintaining robust cybersecurity is crucial in today’s digital age. As cyber threats become more sophisticated, continuous cyber awareness training for employees is essential. Training employees to be vigilant can be the most significant and cost-effective improvement in a company’s cybersecurity defence. Defend Train offers a comprehensive solution designed to enhance your organisation’s cybersecurity through ongoing, […]
Evidence-Based Security Practices

Expansive compliance frameworks listing hundreds of security measures can be found in may places, from the likes of NIST, ISO and CIS. While great for defining what “good” looks like – which controls give you the most risk
Decoding Cloud Security and Pentests for SME CEOs

In today’s digital landscape, where businesses increasingly rely on cloud services, ensuring the security of your data and systems is paramount.
Unlocking the Power of MFA

Let’s face it, dealing with Multi-Factor Authentication (MFA) can sometimes feel like an inconvenience. But before you dismiss it as a hassle, consider this:
How to stay ahead of Cybercriminals

Welcome to the wild world of emails—a playground where cybercriminals roam freely, preying on unsuspecting victims with cunning tactics
Would a SOC work for my business?

It’s like having a superhero team of security analysts, engineers, and experts working together to shield you from cyber threats.
Insights into the UK’s Proposed Cyber Governance Code

In an era where cybersecurity is a top concern for businesses, many still fail to implement essential security measures
AI Instant Response
In the evolving landscape of cybersecurity, time is of the essence. At FoxTech, we understand this urgency and have realtime response through Defend’s Instant Response feature.


